VPN (Virtual Private Network) is one of the most popular security measure practised by netizens to secure their online identity and privacy. VPNs are great for security, but one of the big reasons many people use one is to mask or change their IP address. It is also a great service to access the geo-blocked contents, and check whether your ISP is throttling your connection. What most of the VPN service providers doesn’t reveal when you subscribe to their services is that you’re not protected from “webRTC IP leak,” unless you manually take actions against it.
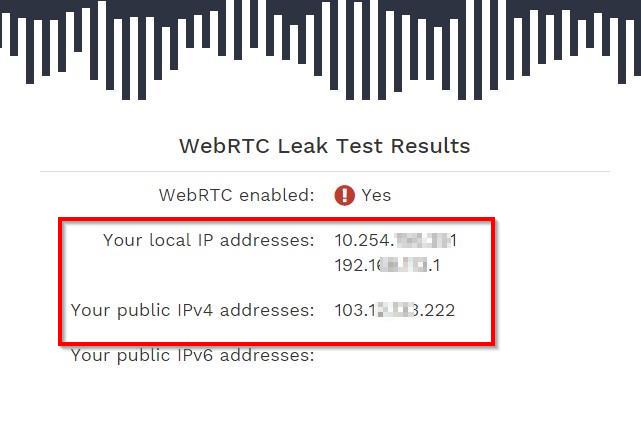
A very concerning security flaw revealed earlier this year that it’s easy to see the real IP-addresses of many VPN users through a WebRTC feature. With a few lines of code, websites can make requests to STUN servers and log users’ VPN IP-address and the “hidden” home IP-address, as well as local network addresses. Advertisers, data brokers, and governments can use it to peek through your VPN to find out where your connection is really coming from.
What is this? Is my privacy at risk?
If you’re using Mozilla Firefox version 22+, Google Chrome version 23+ or any other web browser which are based on these are vulnerable to WebRTC by default. And No, your VPN service providers cannot do anything to fix it.
Actually, WebRTC is an API definition draughted by the World Wide Web Consortium (W3C) that supports browser-to-browser applications for voice calling, video chat, and P2P file sharing without the need for either internal or external plugins. It is enabled on all modern web browsers by default, although it is a really useful piece of programme which enables you to utilise video calling and multimedia transmission right through your browser but due to the nature of this extension, your real IP address and privacy is in danger.
If you’re a VPN user and you didn’t block webRTC on your web browser manually, you’re at great risk. Unfortunately, Most of the VPN providers doesn’t warn you about this vulnerability that poses a higher risk to your privacy.
As far as we know, sites aren’t taking advantage of the flaw yet, but considering services like Hulu, Spotify, Netflix, and others are taking steps to identify and lock out VPN users, it’s not a stretch to assume they’ll start. If you use services like BitTorrent, have a set-top box like a Roku, or just stream music or movies on your computer through a site that’s not available in your country (or you’re an expat and live abroad), the apps and services you use could suddenly stop working.
How to check if your VPN is affected?
 If you’re not using any privacy tools, then this vulnerability won’t affect you. However, if you’re using a VPN service or similar tools to hide your identity than make sure your tool doesn’t leak IP address.
If you’re not using any privacy tools, then this vulnerability won’t affect you. However, if you’re using a VPN service or similar tools to hide your identity than make sure your tool doesn’t leak IP address.
- Deactivate your VPN and check your real IP address – What is my IP Address?
- Now, login to VPN and go to this page – IpLeak test by Hidester, and check if it reveals your real IP address you got from the previous step. You should look at “Your IP address – WebRTC detection.“
- alternatively,
- You can also check if you’re affected by this security flaw using the script shared by a GitHub developer – Daniel Roesler.
How to fix it?
Currently, I am personally using VyprVPN for my next article, reviewing the service they provide. I am glad they warned the users about this security flaw right after it was first reported. The fix is much easier to implement on Firefox because you can disable it without using any third party extension while Chrome users require instaling an extension to disable webRTC in their browser.

Instructions:
Mozilla Firefox:
WebRTC in Mozilla Firefox is partially supported by Firefox 22, and it’s enabled by default. To disable WebRTC in Firefox, go to about:config and toggle media.peerconnection.enabled to false.
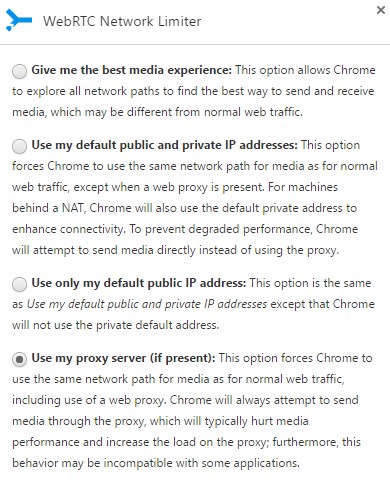
Google Chrome:
WebRTC in Google Chrome is supported and enabled by default since Chrome version 23 (and based on it, ex. Opera, Vivaldi). You cannot disable the webRTC on Google Chrome browsers by default and it can only be achieved using a third party Official Google extension.
This vulnerability is serious, but on the bright side, it’s easily mitigated. If anything, it’s a reminder to never take your privacy for granted, even if you use all the right tools to protect it.
Leave a Reply